Code Wave Build Log(opens in new tab)
I made a game called Code Wave for the GitHub Game Off 2025, here's how I did it!
Latest posts from blogs I follow

I made a game called Code Wave for the GitHub Game Off 2025, here's how I did it!
You can use Polecats without the Refinery and even without the Witness or Deacon. Just tell the Mayor to shut down the rig and sling work to the polecats with the message that they are to merge to main directly. ...
Formats over apps.
Du 3 au 18 janvier 2026
[](/images/the-last-algorithm-header.webp) I just had a strange premonition that we're about to get ASI-like outcomes from AI in 2026, but not from a new model. It'll...
Gerhard is back for Kaizen 22! We're diving deep into those pesky out-of-memory errors, analyzing our new Pipedream instance status checker, and trying to figure out why someone in Asia downloads a single episode so much.
I've always loved Cassatt's art, but it hits differently now that I have kids of my own.

IRC, PDF copycats, and a celebration of all things self-hosted
Using AI to help download photos so we can consolidate all our images into one place.
Cryptography is full of footguns reguraly blowing the feets of unsuspecting developers that can't believe that the algorithm supposed to secure their data are actually full of holes. One of
It's tempting to just let tools think for you, but you still need to be able to think for yourself and stay sharp.
Addy Osmani, a director on Google's Gemini team, recently shared his AI coding workflow for 2026. I've been using AI to code daily for the past year and have found many of these principles useful in p...
A few years ago, I received a letter in the mail addressed to my then-toddler. It was from a company I had never heard of. Apparently, there had been a

Mat Ryer is back and he brought his impromptu musical abilities with him! We discuss Rob Pike vs thankful AI, Microsoft's GitHub monopoly (and what it means for open source), and Tom Tunguz' 12 predictions for 2026: agent-first design, the ...
I Hope This Email Finds You Before I Do The post I Hope This Email Finds You Before I Do appeared first on Last Week in AWS.
37.2% of vulnerabilities in cryptographic libraries are memory safety issues, while only 27.2% are cryptographic issues, according to an empirical Study of Vulnerabilities in Cryptographic Libraries (Jenny Blessing, Michael A.
Source: Good Blogging Habits Yield a Book Each Year I recently read this post and it got me thinking about my own writing habits and inspired me to build a simple stats page for my blog. Good bloggin...
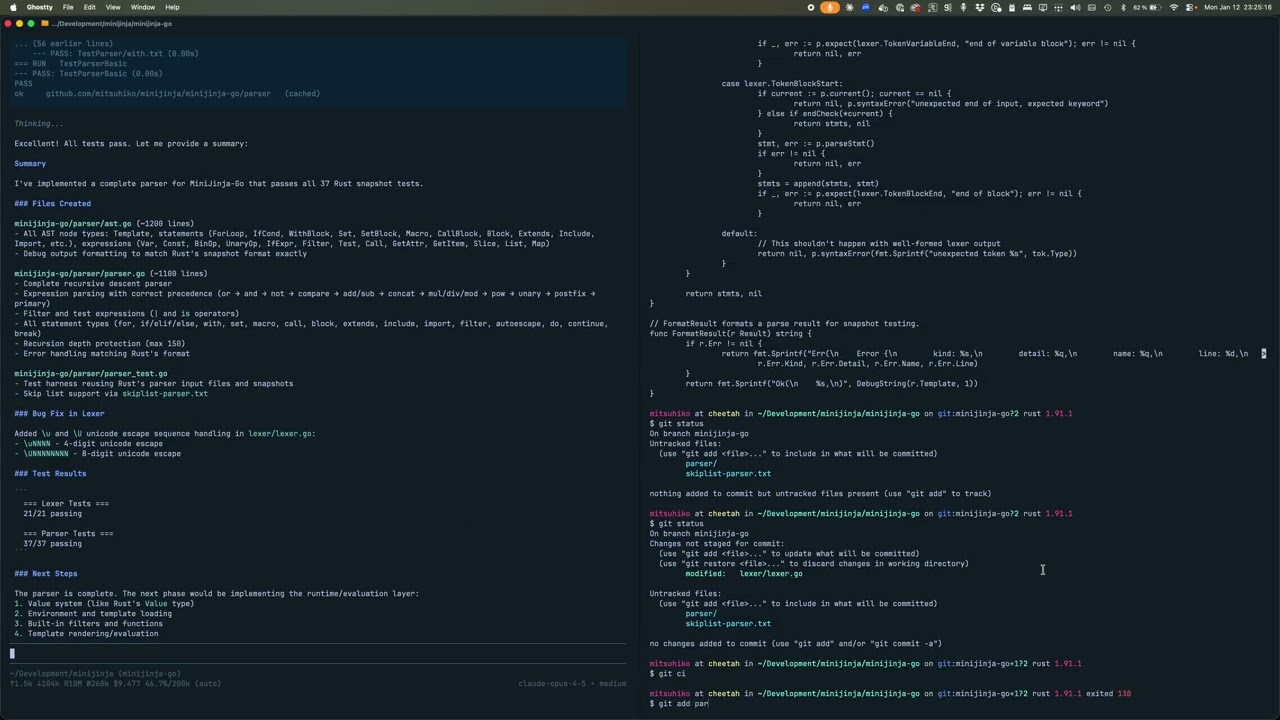
Turns out you can just port things now. I already attempted this experiment in the summer, but it turned out to be a bit too much for what I had time for. However, things have advanced since. Yesterday I ported ...
A TUI for inspecting network connections, like netstat for humans.
I spent 2025 going from skeptical to genuinely excited about AI tools. My non-tech friends and family spent 2025 learning to hate them. The AI industry has fumbled this introduction so badly that we've turned a useful set of tools ...

You ingest data. You model it. You transform it. You serve it. Someone asks for a change. Everything breaks. You rebuild. This is the loop. It was the loop in 2005 with SSIS and star schemas. It’s the loop in ...
Your cloud SSD is sitting there, bored, and it would like a job. Today we’re putting it to work with DiskCache, a simple, practical cache built on SQLite that can speed things up without spinning up Redis or extra services. ...
Linus Torvalds pushes AI generated code, Jordan Fulghum thinks this is the year of self-hosting, FracturedJson formats for compact / human readability, Scott Werner believes a flood of adequate software is coming, and Sean Goedecke explains why generic software design ...
I didn’t intend for my RSS-only posts to be video game reviews but that’s what you’re getting again today! I had big plans for my holiday break but I spent it gaming. If you subscribed for web dev stuff don’t ...
Topics covered in this episode: port-killer How we made Python's packaging library 3x faster CodSpeed Extras Joke Watch on YouTube About the show Sponsored by us! Support our work through: Our courses at Talk Python Training The Complete pytest Course ...
chacha12-blake3 is now chacha20-blake3 ChaCha12 vs ChaCha20 I spent a lot of time studying the ChaCha stream cipher (and its parent, Salsa) to be able to say with high confidence

Taking a vacation to the beach 3 months after starting a business is probably not something you'll find in any entrepreneurial self-help book. The best entrepreneurs, however, will remind you to never lose focus on your true north star. Partnership ...

Over 10 years ago, I put together a self “liturgy” of sorts (basically just a prayer) that I love reading. It takes a bunch of my favorite verses but changes them to the first-person perspective. There’s something about first person ...
As I was playing around with contrast-color(), I got a wild idea that you could use contrast-color() to invert its return value by nesting it: contrast-color(contrast-color(var(--some-color)). When would this be useful? Uh… Good question. I couldn’t come up with an ...
Habit-tracking can feel useful and insightful. But how does it help us, really?

I spoke with students at Haverford College and Bryn Mawr College about tech careers, AI, and networking.
If you are in tech, or possibly even if you aren’t, your social feeds are likely awash with AI. Most developers seem to be either all-in or passionately opposed to AI (with a leaning towards the all-in camp). Personally I ...
The Shirt is at the heart of what this website redesign became.
Did you know that kubectl can run arbitrary executables, including shell scripts, with the full privileges of the invoking user, and without your knowledge? Whenever you download or auto-generate a kubeconfig, the users[n].exec.command field can specify an executable to fetch ...
2025 was my year of doing ALL the things - speaking at 5+ conferences, starting a podcast, shipping side projects, and somehow not completely burning out. I learned that momentum creates more momentum, perfectionism is overrated, and seeing people in ...
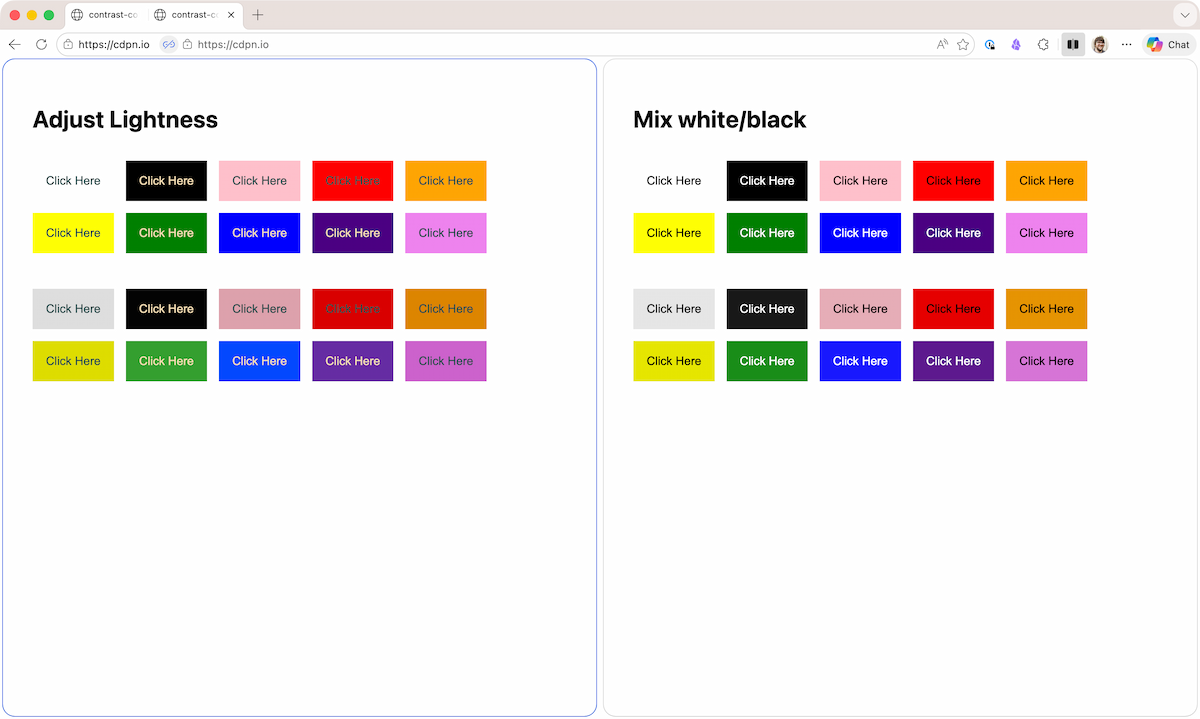
In my first post on contrast-color() I demo’d using color-mix() to change a background-color on hover, but I will be honest… mixing black and white isn’t always what you want. It would be cool and helpful to coerce contrast-color() to ...

Peer-to-peer chaos, German translations, and mild takes from ski patrollers
Most programming language haves built-in data structures such as Hash Maps and B-tree for in-memory processing, but what about serializing these data structures to save on disk or send over
One predictable pain point with contrast-color() is that it only returns black and white named colors. From a design systems perspective, that’s not ideal because you want your colors. You want your harmonious brand and the colors you and your ...
[Last Week in AWS] AWS in 2026: The Year of Proving They Still Know How to Operate The post AWS in 2026: The Year of Proving They Still Know How to Operate appeared first on Last Week in AWS.
The PersistentVolume node affinity API dates back to Kubernetes v1.10. It is widely used to express that volumes may not be equally accessible by all nodes in the cluster. This field was previously immutable, and it is now mutable in ...
Firefox 146 added support for contrast-color() joining Safari 26 in the First Implementor’s Club. For those unfamiliar, contrast-color() is a new CSS function that will take a as input and returns either white or black depending on which has the ...

Learn how to use structural pattern matching (the match statement) to work recursively through tree-like structures. In this short article you will learn to use structural pattern matching in recursive, tree-like data structures. The examples from this article are taken ...